A critique of the go language from the point of view of a backend developer.
Continue reading
Cross-correlation is a useful method that can determine the offset between 2 similar signals. We show an intuitive explanation and a Julia language implemenatation that finds the offset of 2 different recordings of the same song.
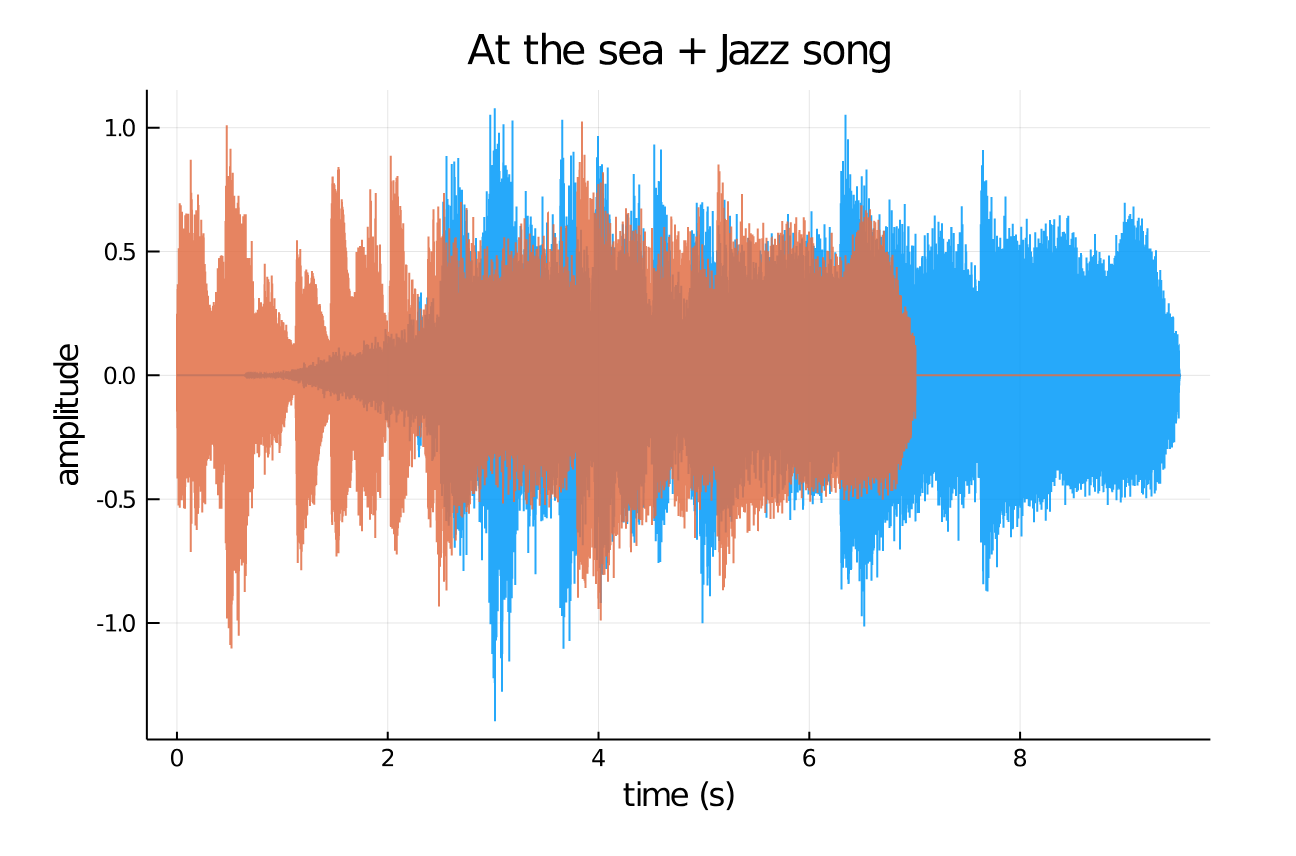
Continue reading
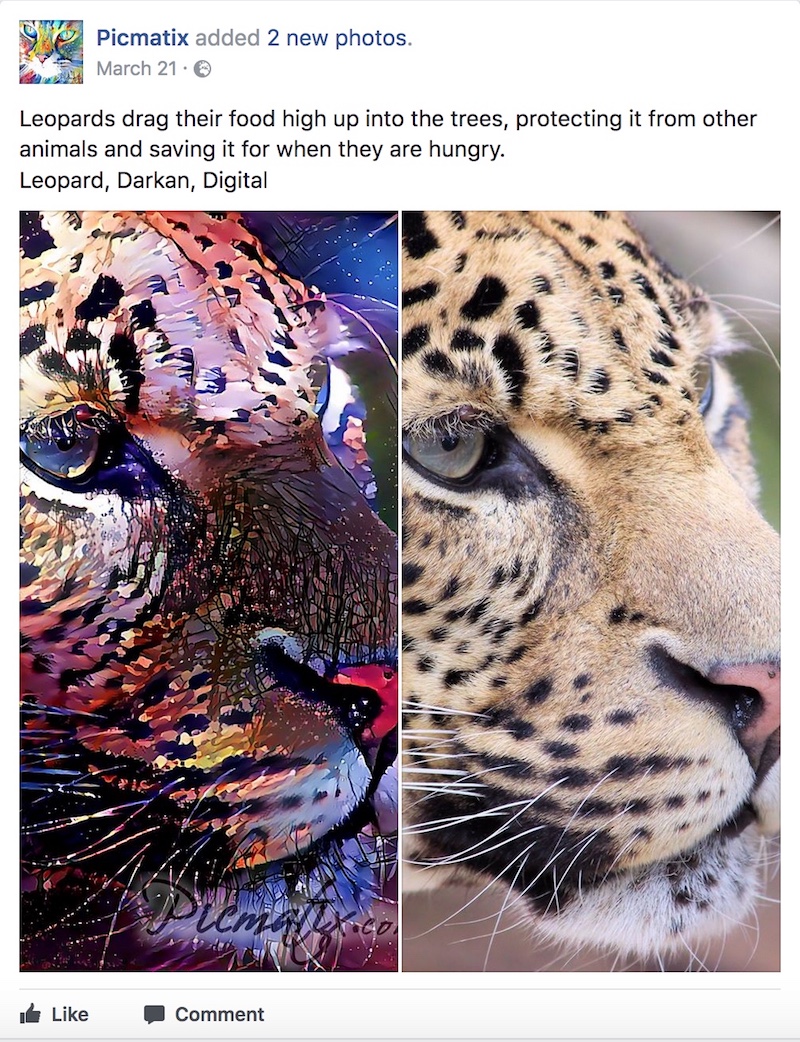
Picmatix.com is an online tool that creates digital art by transferring styles to user pictures. This blog post outlines the serverless architecture that powers the website.
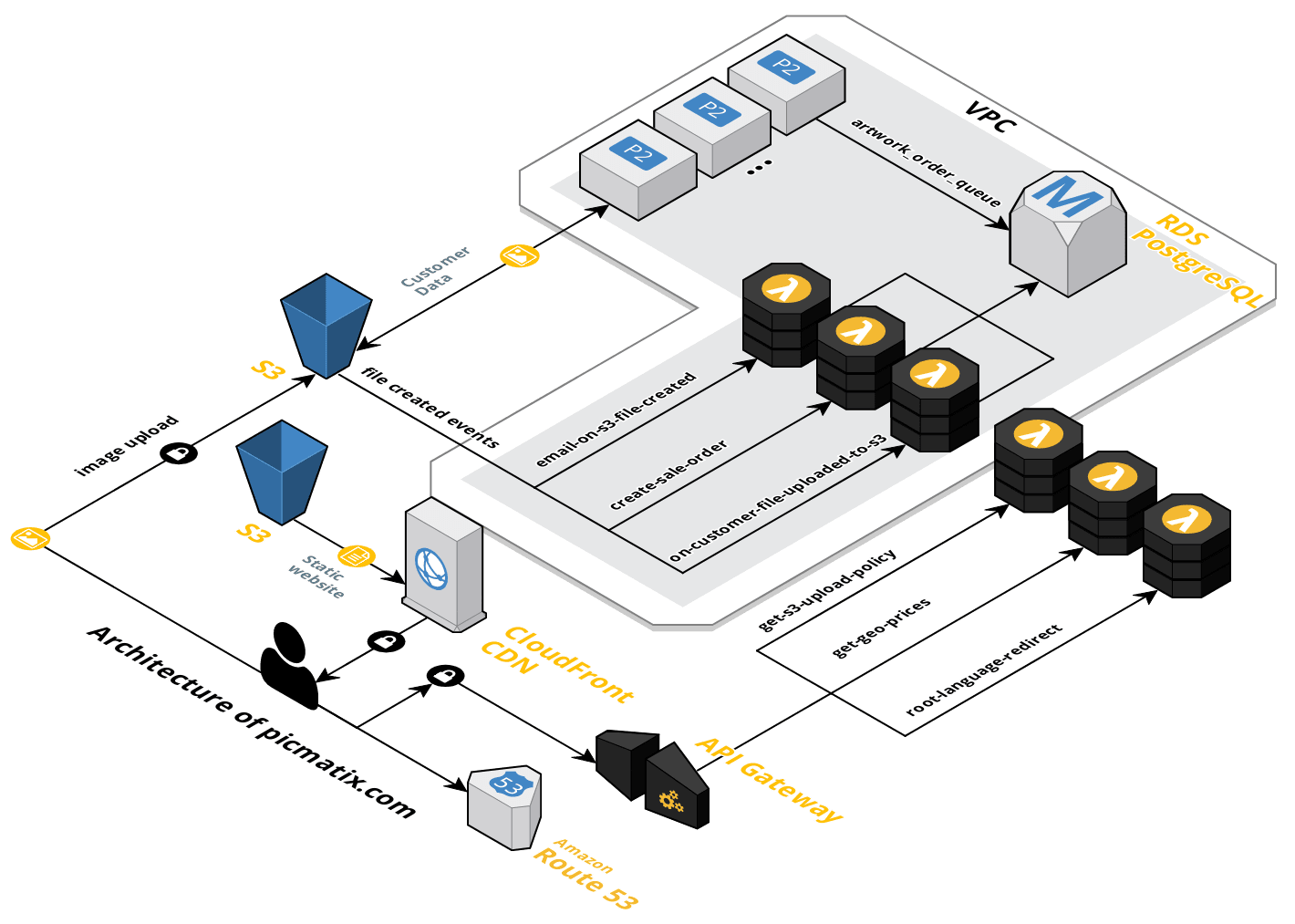
Continue reading
We, as humans, can accurately and precisely tell whether a picture depicts a bird or not by just having a quick glimpse at it. Computers, on the other hand, can hardly see anything meaningful in the collection of 1’s and 0’s that make a virtual image. Not long ago, these kind of visual recognition tasks that humans naturally excel at were extremely difficult for computers to even attempt to do.
Continue reading
Picmatix, a Machine Learning company focused on getting things done. Let’s talk.

Continue reading
Dear reader,
I’m moving my blog to rodrigo.red where I’ll write about the intersection between machine learning, artificial intelligence and humans. If you are interested in these topics, feel free to follow my new blog at https://rodrigo.red/blog/
Continue reading
After taking the course CS7032: Agents, AI & Games at Trinity College, Dublin. We were asked to design and implement an artificial intelligence algorithm for the famous PacMan game, under the rules of pacman-vs-ghosts.net (Which seems to be down as of now) and using our knowledge of abstract architectures.
Continue reading
The WordPress.com stats helper monkeys prepared a 2012 annual report for this blog.
Here’s an excerpt:
Click here to see the complete report.

Continue reading
WebGL
Web browsers are probably the most widely used software in desktops and mobile computers. They have become the swiss army knife of the Web 2.0 digital world and it is under this context that a Javascript API for rendering GPU-based graphics was born: WebGL.

Continue reading
Who’s guilty ?
Both Firefox and Windows are to blame for.
Firefox
Firefox simplifies the process of finding the target function PR_Write as it is inside a dll, compromising the security of the web browser.
Windows
Windows lets our malicious FormGrabber interfere with the normal Firefox’s workflow without asking any questions. It lets our process execute code within Firefox’s Virtual Address Space and more importantly it lets our malicious process change segments of Firefox code.
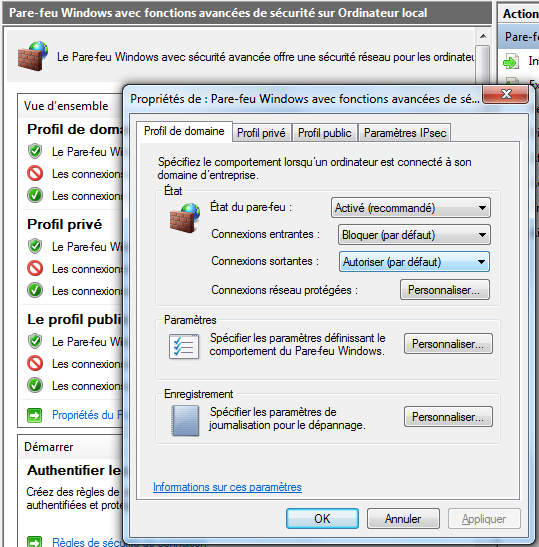
Continue reading